Trezor Login: Ultimate Guide to Secure Crypto Access
Discover step-by-step instructions, pro tips, and advanced strategies to log in safely and protect your cryptocurrency using Trezor hardware wallets.
Why Trezor Login Is Essential
Logging into your Trezor wallet isn’t just about entering credentials. It’s the gatekeeper to your private keys, keeping your crypto safe from hacks, phishing, and malware. Think of it as a digital vault with only you holding the keys.
Step-by-Step Trezor Login
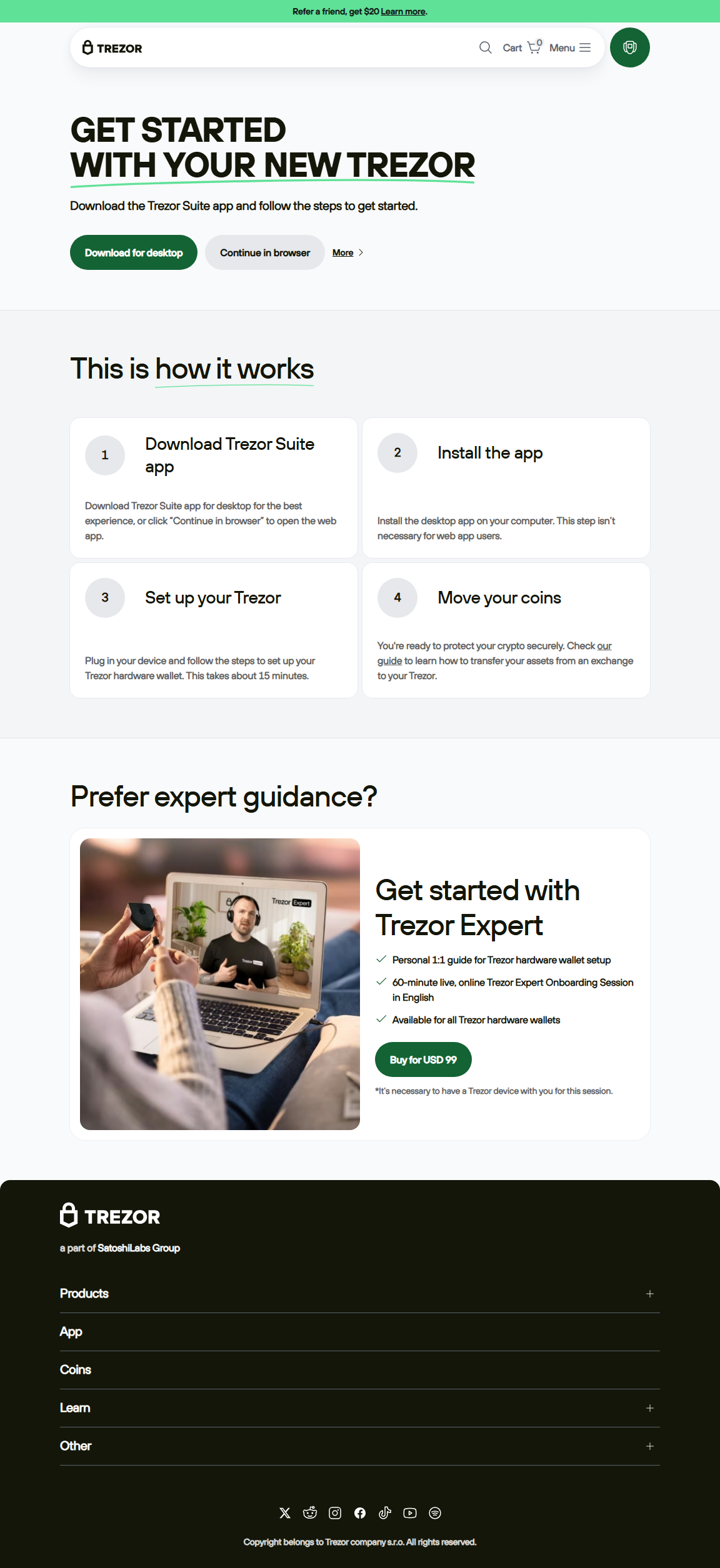
Step 1: Open Trezor Suite
Download the official Trezor Suite on desktop or mobile. This is your secure interface for login and crypto management.
Step 2: Connect Your Device
Plug your Trezor hardware wallet into your device. Follow on-screen instructions for a secure connection.
Step 3: Enter PIN
Input your PIN directly on the device. The randomized keypad ensures protection against keyloggers.
Step 4: Access Wallet
After correct PIN entry, access your wallet to manage crypto, send/receive coins, and view balances securely.
Security Best Practices
- Always use official Trezor Suite or web portals.
- Never enter your recovery seed online.
- Enable passphrase protection for extra security.
- Keep firmware updated.
- Login only from trusted personal devices.
Trezor Login vs Other Wallets
| Feature | Trezor Login | Hot Wallet | Exchange Wallet |
|---|---|---|---|
| Security | Offline + PIN | Online only | Exchange controlled |
| Recovery | Seed phrase | Password only | Exchange process |
| Best Use | Long-term secure storage | Daily transactions | Trading access |
FAQs
No. Physical device is required for PIN verification and secure access.
You must reset your Trezor and restore the wallet using your recovery seed.
Strongly discouraged. Use trusted personal devices to prevent malware or keyloggers.
Conclusion
Mastering Trezor Login guarantees your cryptocurrency remains safe and fully under your control. Follow these steps and best practices to log in securely and manage your crypto confidently.